Case Level Permissions: Difference between revisions
No edit summary |
No edit summary |
||
| (14 intermediate revisions by the same user not shown) | |||
| Line 1: | Line 1: | ||
In addition to [[Roles_and_Permissions|project level permissions]], it's possible to set '''case level permissions''' for models, where visibility can be defined for each case separately based on rules. Usually the rules are based on case attribute values. Case level permissions are effective for all users, but users who have the '''GenericWrite''' permission, can change the case permissions setting for a model and thus change the case permissions. | |||
== Setting up== | |||
Case level permissions are configured in the model properties (can be opened in the models list in the header) in the '''Case Level Permissions''' tab. The following settings are available: | |||
* '''Initialization expression''': [[QPR_ProcessAnalyzer_Expressions|Expression]] that is run only once and can be used as initializing needed objects. This expression can be used to improve performance when part of the Case or EventLogKey expressions are common and thus they don't need to be calculated again for every Case separately. | |||
* '''Permissions expression''': Expression determining which cases the accessing user can see. The expression is evaluated for each case (in the case context). If the evaluation results ''true'', the case is visible for the user; otherwise not. The evaluation is done when no existing eventlog if found based on the ''Eventlog key'' and a new eventlog needs to be generated. This expression is mandatory for the case level permissions to work | |||
* '''Eventlog key expression''': Expression used to generate a uniquely identifying string for the eventlogs when the case level permissions are in use. If a cached eventLog with the same key already exists in the system, that eventlog is used instead of creating a new. | |||
== Configuration examples == | |||
Visibility of cases is limited in a way that only those users can see cases belonging to a group which name is same as the ''Region'' (case attribute). | |||
* Initialization expression: '''let groupNames = OrderByValue(CurrentUser.GroupNames)''' | |||
* Permissions expression: '''Region.In(groupNames)''' | |||
* Eventlog key: '''StringJoin("_", groupNames)''' | |||
| | Cases are only visible for users whose user name is same as the ''Account Manager'' (case attribute): | ||
* Initialization expression: '''let userName = CurrentUser.Name''' | |||
* Permissions expression: '''Attribute("Account Manager") == userName''' | |||
* Eventlog key: '''CurrentUser.Id''' | |||
Cases where ''Region'' case attribute is ''Dallas'' will only be visible for users belonging to group ''GroupA'' (and ''New York'' for group ''GroupB''): | |||
* Initialization expression: '''let groupNames = CurrentUser.GroupNames''' | |||
* Permissions expression: '''(Region == "Dallas" && "GroupA".In(groupNames)) || (Region == "New York" && "GroupB".In(groupNames))''' | |||
* Eventlog key: '''If("GroupA".In(groupNames), "_A", "_") + If("GroupB".In(groupNames), "_B", "_")''' | |||
User ''qpr'' can only see cases where ''Region'' is ''Dallas'', and all other users can see all cases: | |||
* Initialization expression: '''let userName = CurrentUser.Name''' | |||
* Permissions expression: '''(userName == "qpr" && Attribute("Region") == "Dallas") || userName != "qpr"''' | |||
* Eventlog key: '''CurrentUser.Id''' | |||
== | == Use case == | ||
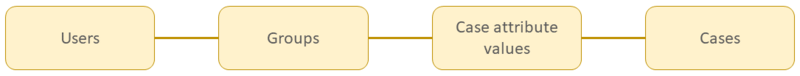
Case level permissions | Case level permissions can be implemented with the principle illustrated in the image below. ''Users'' already belong to certain ''groups'' in the user management, and ''cases'' have certain ''case attribute values'' which is part of the loaded process mining data. Additionally, the linkage between case attribute values (of a certain case attribute) and groups needs to be defined when this security feature is configured. The image below illustrates the chain between ''users'' and ''cases'', how certain users are able to see certain cases when viewing analyses from a QPR ProcessAnalyzer model. | ||
[[File:CasePermissions.png|800px]] | [[File:CasePermissions.png|800px]] | ||
| Line 63: | Line 76: | ||
There is no way for a user to be aware of the existence of cases that the user doesn't have rights to. | There is no way for a user to be aware of the existence of cases that the user doesn't have rights to. | ||
[[Category: QPR ProcessAnalyzer]] | [[Category: QPR ProcessAnalyzer]] | ||
Latest revision as of 19:30, 11 December 2021
In addition to project level permissions, it's possible to set case level permissions for models, where visibility can be defined for each case separately based on rules. Usually the rules are based on case attribute values. Case level permissions are effective for all users, but users who have the GenericWrite permission, can change the case permissions setting for a model and thus change the case permissions.
Setting up
Case level permissions are configured in the model properties (can be opened in the models list in the header) in the Case Level Permissions tab. The following settings are available:
- Initialization expression: Expression that is run only once and can be used as initializing needed objects. This expression can be used to improve performance when part of the Case or EventLogKey expressions are common and thus they don't need to be calculated again for every Case separately.
- Permissions expression: Expression determining which cases the accessing user can see. The expression is evaluated for each case (in the case context). If the evaluation results true, the case is visible for the user; otherwise not. The evaluation is done when no existing eventlog if found based on the Eventlog key and a new eventlog needs to be generated. This expression is mandatory for the case level permissions to work
- Eventlog key expression: Expression used to generate a uniquely identifying string for the eventlogs when the case level permissions are in use. If a cached eventLog with the same key already exists in the system, that eventlog is used instead of creating a new.
Configuration examples
Visibility of cases is limited in a way that only those users can see cases belonging to a group which name is same as the Region (case attribute).
- Initialization expression: let groupNames = OrderByValue(CurrentUser.GroupNames)
- Permissions expression: Region.In(groupNames)
- Eventlog key: StringJoin("_", groupNames)
Cases are only visible for users whose user name is same as the Account Manager (case attribute):
- Initialization expression: let userName = CurrentUser.Name
- Permissions expression: Attribute("Account Manager") == userName
- Eventlog key: CurrentUser.Id
Cases where Region case attribute is Dallas will only be visible for users belonging to group GroupA (and New York for group GroupB):
- Initialization expression: let groupNames = CurrentUser.GroupNames
- Permissions expression: (Region == "Dallas" && "GroupA".In(groupNames)) || (Region == "New York" && "GroupB".In(groupNames))
- Eventlog key: If("GroupA".In(groupNames), "_A", "_") + If("GroupB".In(groupNames), "_B", "_")
User qpr can only see cases where Region is Dallas, and all other users can see all cases:
- Initialization expression: let userName = CurrentUser.Name
- Permissions expression: (userName == "qpr" && Attribute("Region") == "Dallas") || userName != "qpr"
- Eventlog key: CurrentUser.Id
Use case
Case level permissions can be implemented with the principle illustrated in the image below. Users already belong to certain groups in the user management, and cases have certain case attribute values which is part of the loaded process mining data. Additionally, the linkage between case attribute values (of a certain case attribute) and groups needs to be defined when this security feature is configured. The image below illustrates the chain between users and cases, how certain users are able to see certain cases when viewing analyses from a QPR ProcessAnalyzer model.
Example: There are groups G1, G2 and G3. Case permissions have been set as follows:
- group G1 can only see cases where (case attribute) Region is Dallas
- group G2 can only see cases where Region is Austin
- group G3 can only see cases where Region is either Austin or New York
QPR ProcessAnalyzer model contains the following cases:
| Case name | Region (case attribute) | Groups can see |
|---|---|---|
| A | Dallas | G1 |
| B | Dallas | G1 |
| C | Austin | G2, G3 |
| D | New York | G3 |
| E | New York | G3 |
| F | New York | G3 |
Thus, when viewing analyses, a user see that the model contains the following cases:
- If the user belongs to group G1 only, the user can see cases A and B (2 cases)
- If the user belongs to group G2 only, the user can see case C (1 case)
- If the user belongs to group G3 only, the user can see cases C, D, E and F (4 cases)
- If the user belongs to groups G1 and G2 only, the user can see cases A, B and C (3 cases)
There is no way for a user to be aware of the existence of cases that the user doesn't have rights to.